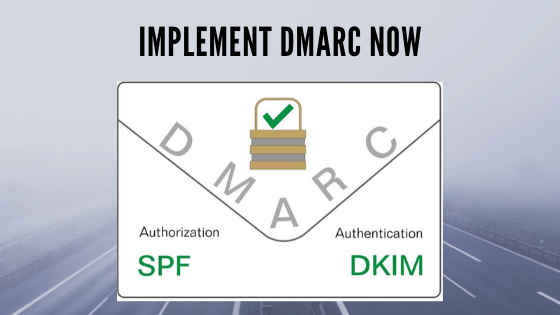
Organizations can stop spoof emails impersonating as them from reaching their customer’s inbox or junk/bulk folder by enabling DMARC.
Email Security
Organizations can stop spoof emails impersonating as them from reaching their customer’s inbox or junk/bulk folder by enabling DMARC.
Venkata Satish Guttula, Director – Security, Rediff.com India Ltd, has won an Award under the category Data Security (Infrastructure Engagement) at the DataCenter Summit and Awards 2018. DataCenter Summit and Awards 2018 is the 6th edition, held on 5th October 2018 at The St. Regis, Mumbai, organised & produced By USB Forums. DataCenter Summit and Awards is India’s largest, most influential gathering of industry expertise to discuss the evolving landscapes of datacenters and to keep them more relevant to the changing needs.
With 450+ Delegates, 93+ Speakers, 50+ partners & 45+ Keynote Sessions, it’s bound to be a big event.
Spear phishing is used when a hacker targets specific people using a more personalized approach. Spear Phishing attacks can be highly effective, because the perpetrators use tailored language to target each individual. Conventional Anti Spam engines have been successful in fighting mass spam emails as they derive recurring patterns & phishing URLs by using information from previously identified threats. Such techniques are completely ineffective in identifying the ‘one-off targeted Spear Phishing attacks’. Read on to demystify mystery that surrounds threats of Spear Phishing attacks and the approach to mitigate them.

Your brand reputation can be at risk. Cyber criminals can exploit the weaknesses in email security and impersonate your brand to send phishing emails. Thanks to DMARC, you can protect your brand’s identity and keep phishers at bay. Read on to figure out how DMARC works and what is in it for you.

This is the second edition of the cyber security show & awards, an event by Trescon on 20th September 2018 at The Leela Mumbai. Rediffmail Enterprise is proud to be the PLATINUM PARTNER for the event.
For most of the companies, over 70% of your business critical information reside in your emails and there are many ways by which mail data can be leaked electronically from a company like inappropriately printed info, copying to pen drive, writing the data to a DVD/ CD or any other portable storage device.