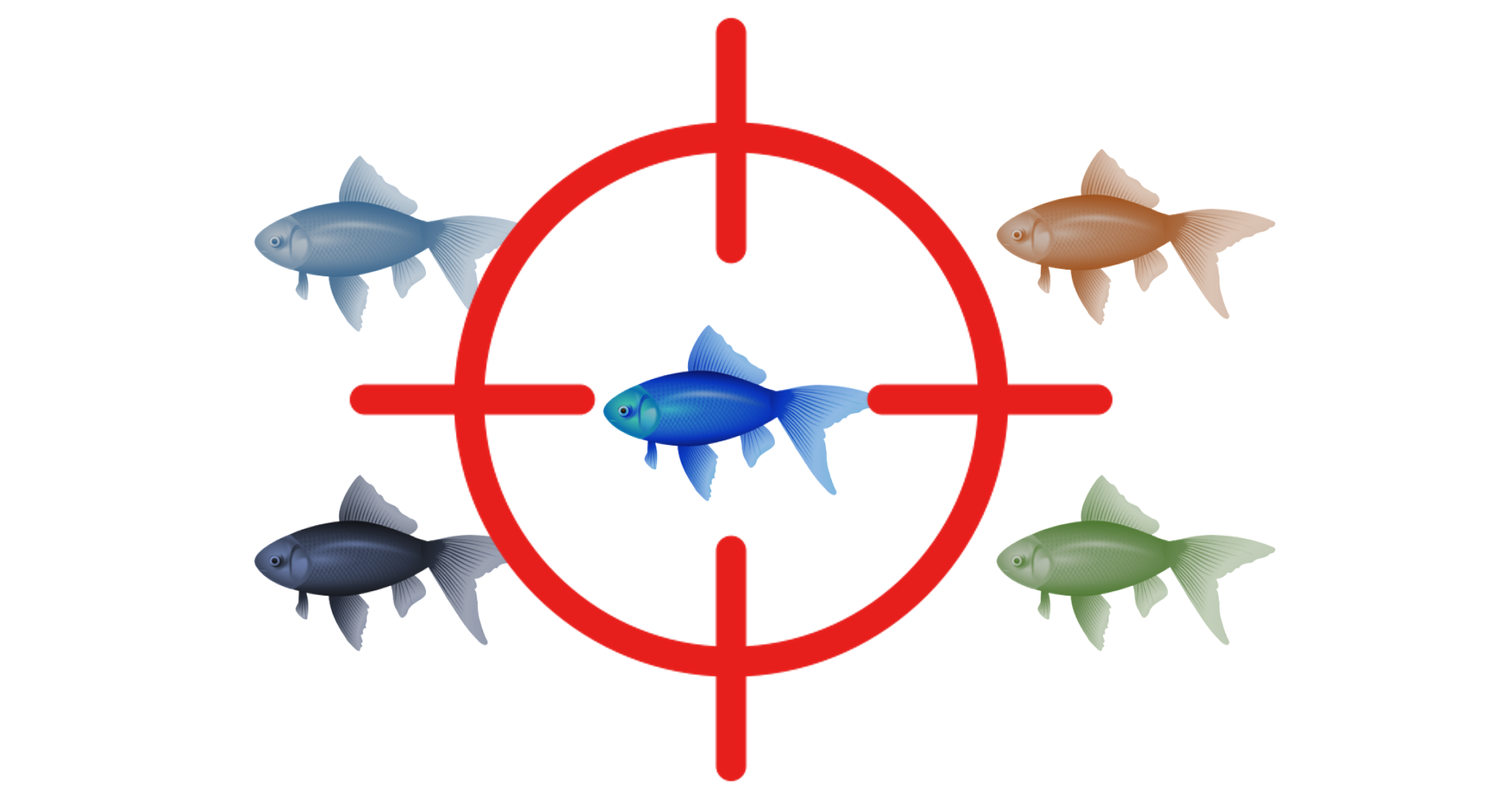
Spear phishing is used when a hacker targets specific people using a more personalized approach. Spear Phishing attacks can be highly effective, because the perpetrators use tailored language to target each individual. Conventional Anti Spam engines have been successful in fighting mass spam emails as they derive recurring patterns & phishing URLs by using information from previously identified threats. Such techniques are completely ineffective in identifying the ‘one-off targeted Spear Phishing attacks’. Read on to demystify mystery that surrounds threats of Spear Phishing attacks and the approach to mitigate them.